
Customizing onboarding of guests and IoT devices is easy and secure with predefined templates for non-IT personnel
Enables consistent policy roll-out across the entire network
Enhances security with agent-based and agentless assessment option
Several tools for wired and wireless
Cumbersome onboarding
Limited profiling
Simple policies
Rudimentary IoT management
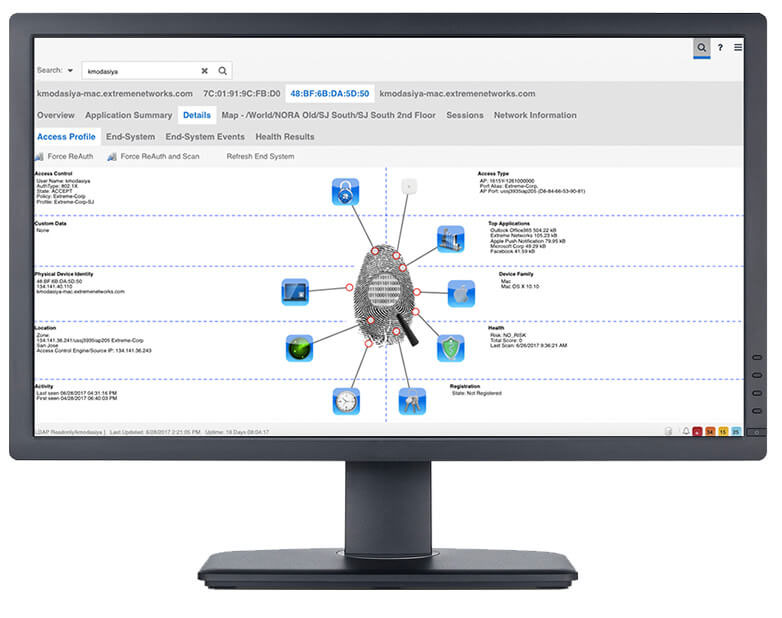
Single pane of glass for wired and wireless
Secure, simple onboarding
Detailed profiling with access and app analytics data
Context-based policies
Policies based on security posture of IoT devices