

Advanced Windows and Linux protection and visibility across your cloud, on-premises, and virtual server workloads.
Go beyond the server by incorporating cross-product data source for even more visibility.
Ransomware file protection, automatic file recovery, and behavioral analysis stops ransomware and boot record attacks.
Artificial intelligence built into Intercept X that detects both known and unknown malware without relying on signatures.
Deny attackers by blocking the exploits and techniques used to distribute malware, steal credentials, and escape detection.
Elite team of threat hunters and response experts who take targeted actions on your behalf to neutralize even the most sophisticated threats.
Detect cloud security and compliance configuration risk, anomalous activity, vulnerabilities, and misconfigurations.
Prevent unauthorized programs running on your servers and receive notification if attempts are made to tamper with critical files.
Identify sophisticated attacks as they happen without requiring a kernel module, orchestration, baselining, or system scans.
*See the Linux datasheet for details on Linux capabilities
See Technical SpecificationsSophos Cloud Workload Protection provides complete visibility into your host and container workloads, identifying malware, exploits, and anomalous behavior before they get a foothold.
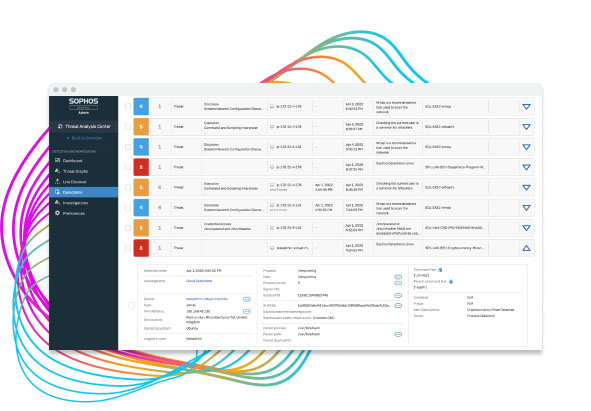
Extended detection and response (XDR) provides complete visibility of hosts, containers, endpoints, the network, and even cloud provider native services
Cloud-native behavioral and exploit runtime detections identify threats including container escapes, kernel exploits, and privilege escalation attempts
Streamlined threat investigation workflows prioritize high-risk incident detections and consolidate connected events to increase efficiency
Integrated Live Response establishes a secure command line terminal to hosts for remediation
Flexible, lightweight server host and container protection is optimized for performance. Available as an agent or via API for Linux to integrate with your security operations, IT, and DevOps processes.

Secure the host and container with an agent managed from the Sophos Central management console. Easily investigate and respond to behavioral, exploit, and malware threats in one place while increasing IT hygiene with automated detections, intuitive querying, and remote response capabilities.
Fine-tuned for maximum performance, seamlessly enrich your security operations workflows with an ultra-lightweight Linux sensor providing API integration of host and container behavioral and exploit runtime detections into your existing automation, orchestration, log management, and incident response tooling - available soon.
As your organization expands from on-premises or data center to hybrid and multi-cloud environments, Sophos protects your infrastructure and data across deployment and computing models.

Detection and resilience for Linux systems in any environment, including container runtimes such as Docker, containerd, and CRI-O. Our detection is crafted with the threat models of cloud-native systems in mind.

Secure your Windows hosts and remote workers against ransomware, exploits and never-before-seen threats, control applications, lockdown good configurations, and monitor changes to critical system files.

Secure applications and data across your hybrid cloud footprint from a single console. The flexible agent runs on-premises, in data centers, hybrid and multi-cloud environments including AWS, Azure, GCP and Oracle Cloud.
Intercept X for Server uses deep learning, an advanced form of machine learning that detects both known and unknown malware without relying on signatures.
Deep learning makes Intercept X for Server smarter, more scalable, and more effective against never-seen-before threats. Intercept X for Server leverages deep learning to outperform security solutions that use traditional machine learning or signature-based detection alone.


Intercept X for Server includes anti-ransomware capabilities that detect malicious encryption processes and block them before they can spread across your network. Both file-based and master boot record (MBR) ransomware is stopped.
Any encrypted files are rolled back to a safe state so your employees can continue working uninterrupted, minimizing the impact to business continuity. You get detailed post-cleanup information so you can see where the threat got in, what it touched, and when it was neutralized.
Design your cloud environments to meet security best-practice standards with the visibility and tools to maintain them using integrated Sophos Cloud Optix Standard capabilities.
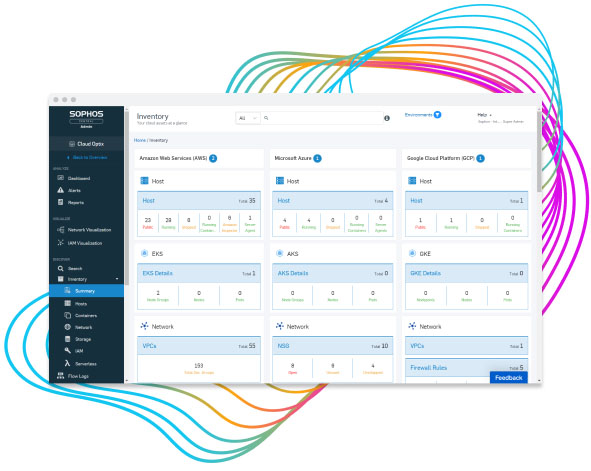
Proactively identify unsanctioned activity and misconfigurations across Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP)
Continuously discover cloud resources with detailed inventory and visibility of Sophos host protection and Sophos Firewall deployments
Automatically overlay security best practice standards to detect gaps in posture, identify quick wins and critical issues
Detect high-risk anomalies in user IAM role behavior, pinpointing unusual access patterns, locations, and malicious behaviors quickly to prevent a breach
Intercept X Advanced for Server with XDR is the industry's only XDR solution that synchronizes native endpoint, server, firewall, email, cloud and O365 security. Get a holistic view of your organization's environment with the richest data set and deep analysis for threat detection, investigation, and response for both dedicated SOC teams and IT admins.
Proactive 24/7 hunting by our elite team of threat analysts. Determine the potential impact and context of threats to your business.
Get actionable advice for addressing the root cause of recurring incidents to stop them from occurring again.
Initiates actions to remotely disrupt, contain and neutralize threats on your behalf to stop even the most sophisticated threats.