
Applies and enforces device profiles, controls IoT device network access. Isolates IoT devices into secure zones.
Works with Fabric Connect to create secure zones that can be deployed quickly and easily at the network edge. Or works over 3rd party networks isolating groups of devices in IPsec tunnels.
Enable non-technical staff to securely on-board, monitor, track and move their devices without burdening already taxed networking and IT teams.
Complex to implement and manage
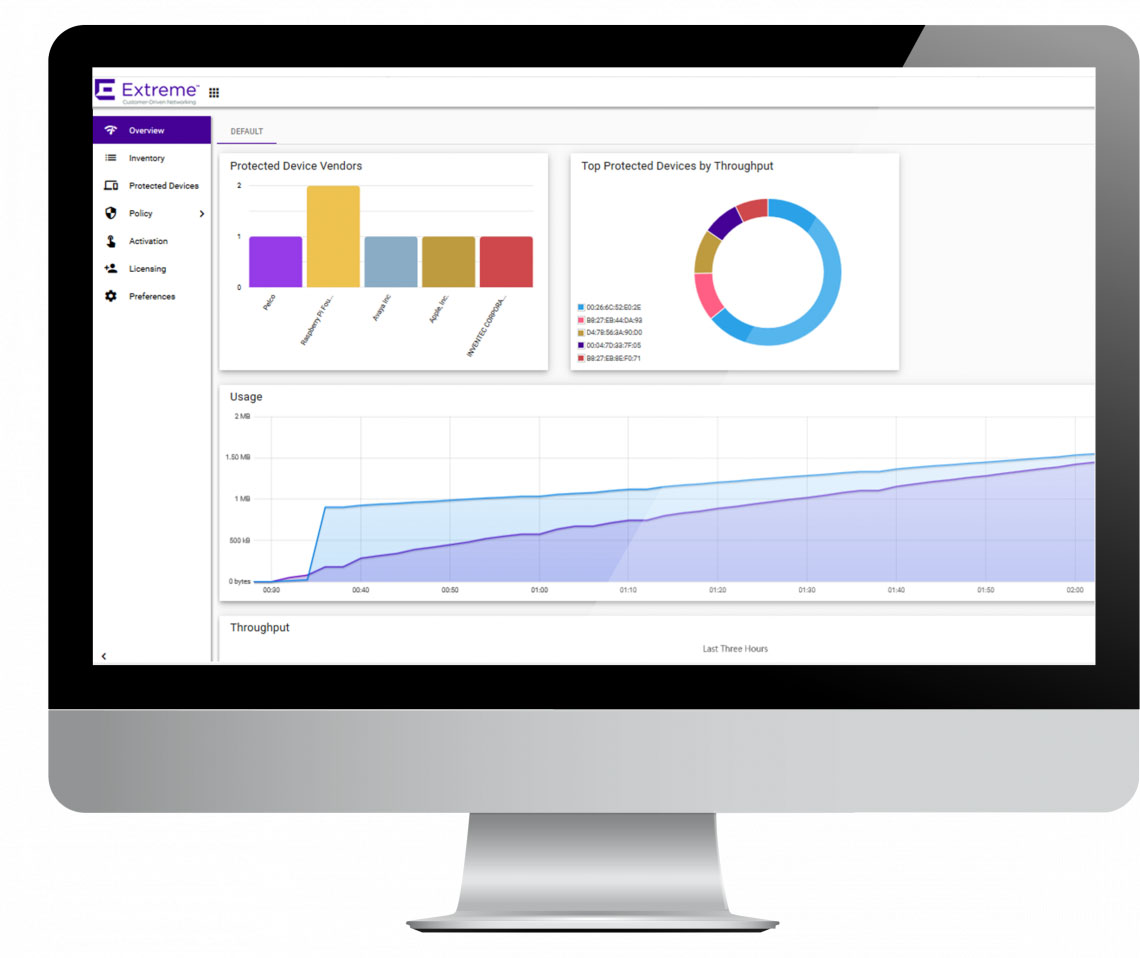
Lack of centralized inventory
Lack of isolation / secure zones
IT intensive
Simple to deploy and manage
Centralized inventory for devices
Secure zones at scale
Leveraged by non-technical staff